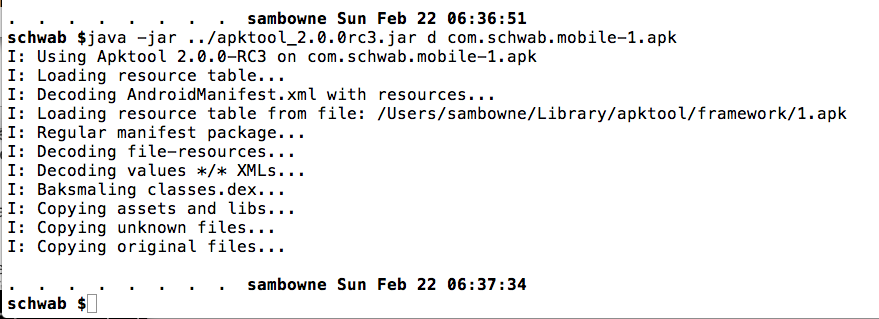
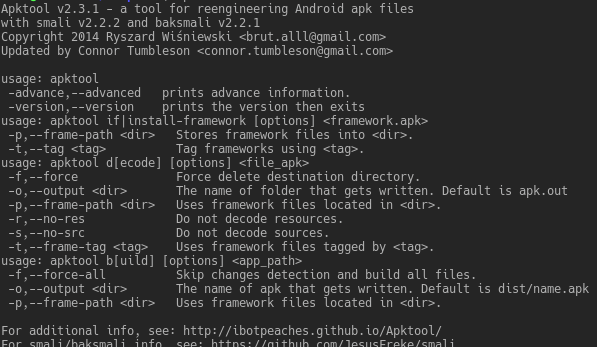
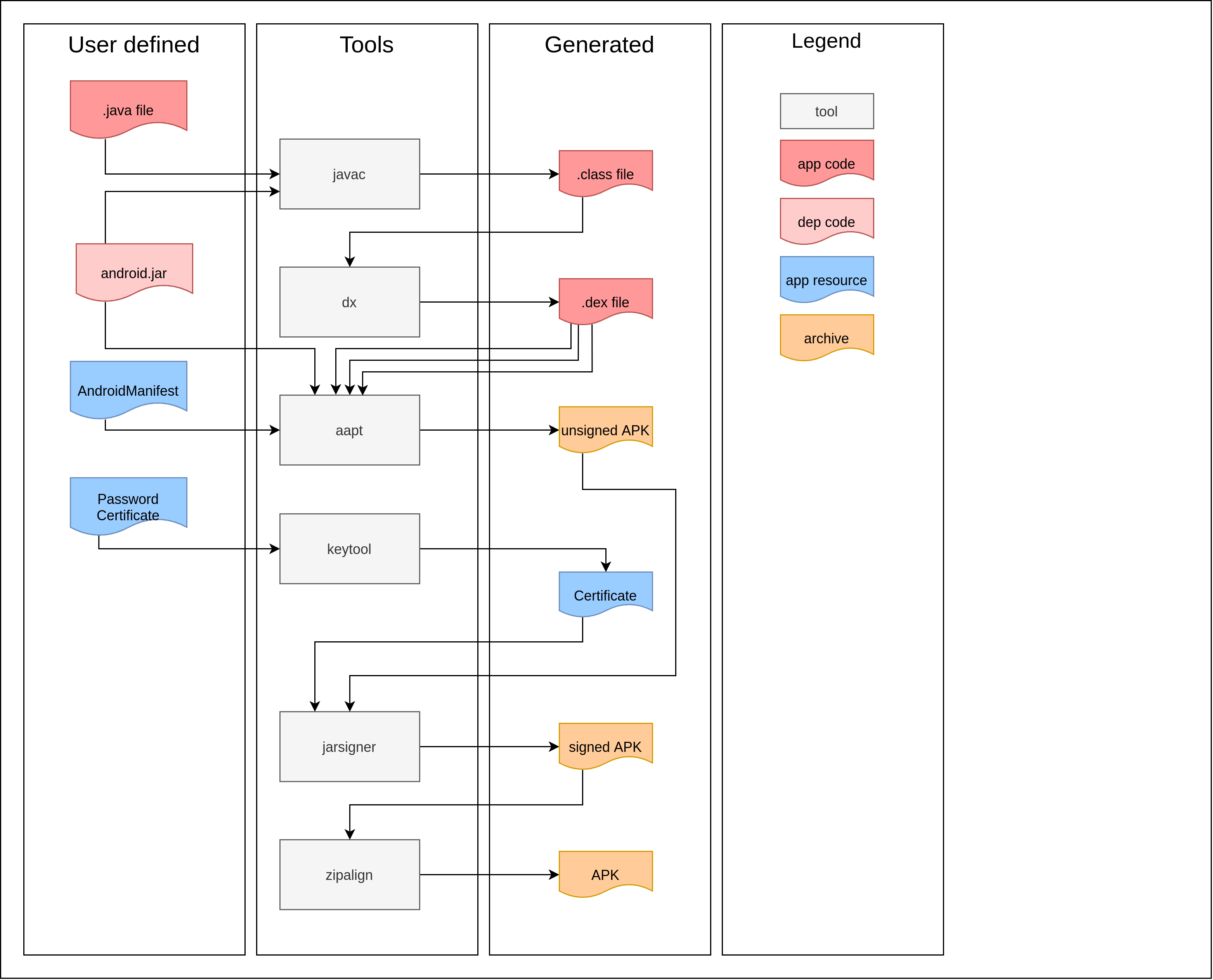
SANS Penetration Testing | Modifying Android Apps: A SEC575 Hands-on Exercise, Part 1 | SANS Institute
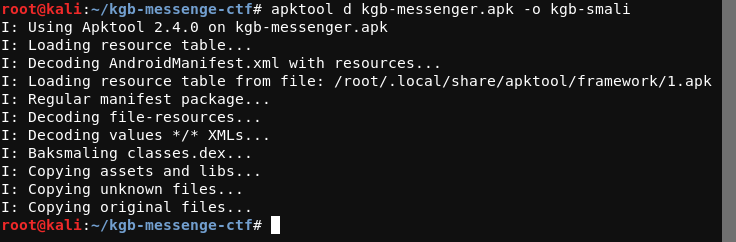
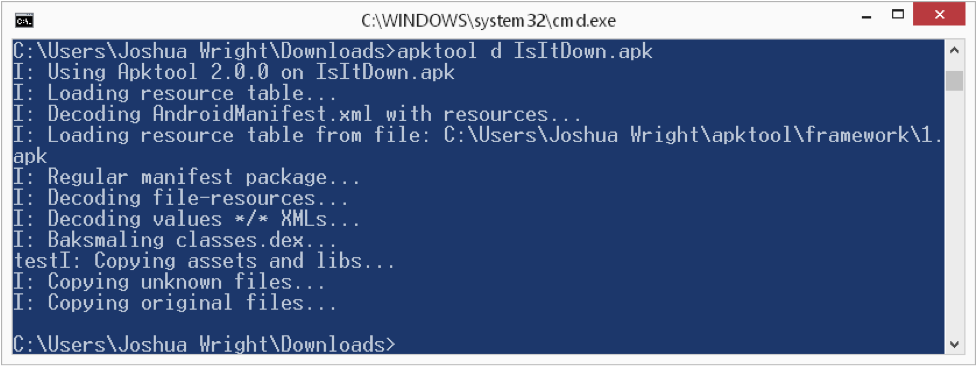
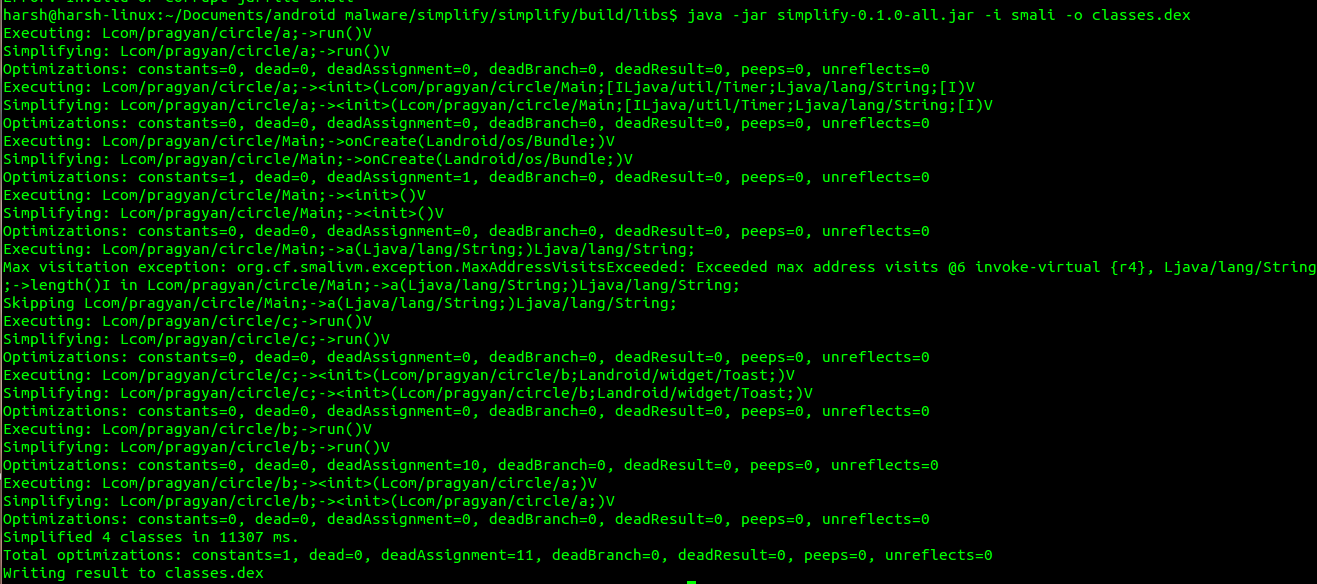
Android CTF — KGB Messenger. This is a write up of an open source… | by Harshit Maheshwari | InfoSec Write-ups
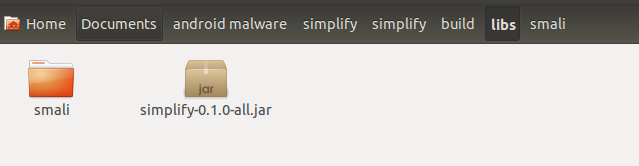
BytecodeViewer - View smali and java code (Cross-platform) - Platinmods.com - Android & iOS MODs, Mobile Games & Apps


![MODULE] Smali Patcher 7.4 | Page 3 | XDA Forums MODULE] Smali Patcher 7.4 | Page 3 | XDA Forums](https://forum.xda-developers.com/proxy.php?image=https%3A%2F%2Fi.imgur.com%2FENMz7e0.png&hash=90e4ecb6a1352f4d43eea9fa6d249186)






![Smali Patcher Magisk Module Latest [Download] Smali Patcher Magisk Module Latest [Download]](https://magiskapp.com/wp-content/uploads/2020/10/Smali-Patcher-1024x576.jpg)
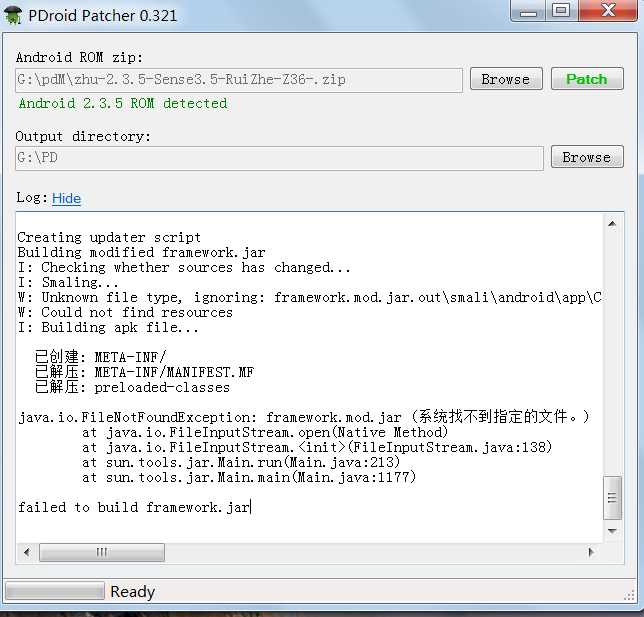
![MODULE] Smali Patcher 7.4 | XDA Forums MODULE] Smali Patcher 7.4 | XDA Forums](https://forum.xda-developers.com/proxy.php?image=https%3A%2F%2Fi.imgur.com%2FaoImM4m.jpg&hash=2240f01ef05216f398d2d734f1ad5044)
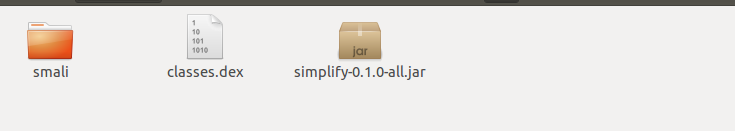
![mini Guide] [Android] [ROOT] Smalli Patcher: Deodexing services.jar : r/PokemonGoSpoofing mini Guide] [Android] [ROOT] Smalli Patcher: Deodexing services.jar : r/PokemonGoSpoofing](https://i.redd.it/kosr1dql2kd21.jpg)